The White House has been in the news over the past two weeks in reports from USA Today, CNN, NBC News, and many more sources. Officials informed NBC News (Mitchell, 2015 April) that it is believed the Russians accessed the system through State Department computers which contained private unpublished schedule of President Obama. While attribution usually takes weeks or months for the FBI’s Cyber Division to determine and publish, the sources of the attacks are less important than the objective. The objective is similar across all of these attacks; to retrieve classified information. According to former FBI official Shawn Henry and the president and CSO of CrowdStrike Services cyber-attacks occur because countries such as China and Russia have the need to look at U.S. polices, how policies are created, new initiatives that are under consideration, basically anything that these foreign countries can get that will provide them with some advantage at the next level of trade talks and collect intelligence against the US for personal gains.
Healthcare organizations need to understand the criticality, reasoning, and determination for these attacks as well. When VIPs such as political or military leaders are seen or treated by their facility, or by a facility they are affiliated or networked with, their systems, networks, and data become a high priority target for foreign threat actors. Healthcare organizations often fail to realize how important their health information data repositories are for reasons entirely Unrelated to identity theft or medical billing fraud. Basic healthcare information about a head of state, a state department official involved in a negotiations process, senior leadership in the military or a congressional committee is incredibly important to both Nation-State actors and Terrorist organizations. Healthcare providers have no idea that cyber-bullets are flying by their ears in this electronic war!
On April 1st, 2015, President Barack Obama sent out an Executive Order titled “Blocking the Property of Certain Persons Engaging in Significant Malicious Cyber-Enabled activities”. Here’s a short excerpt from the Executive Order:
Only a few months ago on January 13th, President Obama announced a legislative National Data Breach Notification standard and miscellaneous cybersecurity legislative proposals and efforts. The Executive Order should provide the U.S. government the tools needed to combat the expanding malicious cyber activities. The Executive Order enables the Treasury Department along with the Attorney General and the Secretary of State to impose sanctions on the unlawful actions created by hackers. The goal would be to freeze targets’ assets when operating in the U.S. financial system and prohibiting them from having transaction with American companies.
Both Public and Government sectors must pay immediate and substantial attention to this existing and evolving threat!
References
Henry.S. (2014, November 17). Cyber attacks hit State department email, web. Retrieved from http://www.cnn.com/videos/bestoftv/2014/11/17/lead-intv-henry-state-department-hacking.cnn
Hollywood Reporter. (2015, April 1). Obama creates federal sanctions to deal with cyber attacks. Retrieved from https://www.youtube.com/watch?v=dNFdUphnU18
Mitchell, A.(2015, April). Russia hacked White House last year, U.S. officials says. Retrieved from http://www.nbcnews.com/news/us-news/russia-hacked-white-house-last-year-u-s-officials-say-n337521
Whitehouse.gov. (2015, April 1). The White House: Executive order. Retrieved from https://www.whitehouse.gov/the-press-office/2015/04/01/executive-order-blocking-property-certain-persons-engaging-significant-m


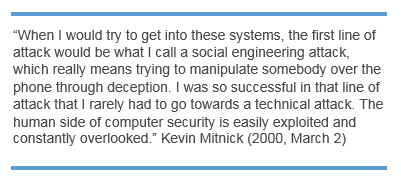
 The attacker might send a false e-mail often that look surprisingly legitimate, and may seem valid. However, it is important to view the URL in the address field which can tell you if the page you have been directed to is not valid. The email might come from a credit card company requesting you to respond and might often come from other types of organizations such as charities during a natural disaster, holidays, etc. Some phishing attacks involve a phone call directly to the target, where the attacker often claims to be another employee, perhaps calling from the I.T. Helpdesk.
The attacker might send a false e-mail often that look surprisingly legitimate, and may seem valid. However, it is important to view the URL in the address field which can tell you if the page you have been directed to is not valid. The email might come from a credit card company requesting you to respond and might often come from other types of organizations such as charities during a natural disaster, holidays, etc. Some phishing attacks involve a phone call directly to the target, where the attacker often claims to be another employee, perhaps calling from the I.T. Helpdesk.

















You must be logged in to post a comment.