It’s been called the worst data breach in U.S. history. Attackers stole half the U.S. population’s social security numbers from Equifax in July, but the company only notified customers in September. The fallout has been devastating, with class action lawsuits being filed and consumers demanding free credit monitoring.
“Equifax has been hit with dozens of lawsuits from shareholders, consumers and now one filed by a small Wisconsin credit union that represents what could be the first by a financial institution attempting to preemptively recoup losses caused by alleged fraud the hack could cause” as reported by the Washington Post.
Equifax provided a website for customers to search if they were affected. However, on multiple occasions, the company’s official Tweeter account directed customers to a fake phishing site instead. See image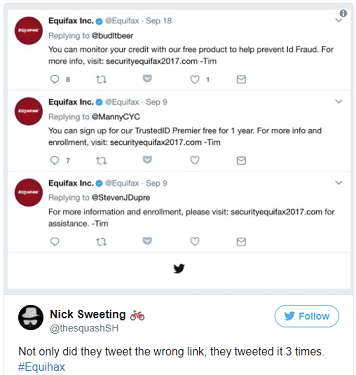
The company’s stock price has fallen 25 percent since they announced the hack Sept. 7 according to ABC news. In the meantime, Equifax had a meeting with investors in New York in hopes to contain the fallout.
To receive information on how to prevent this type of breach visit VirtualAuditor.com
Virtual Auditor’s Virtual Security Officer Server (VSOS) is a unique, fully-managed, information security auditing assessment solution that helps you establish a formal information security program within your organization. VSOS is packed with powerful vulnerability, auditing and testing tools that can help identify security vulnerabilities within your environment, as well as gaps in your existing security program.
Quick tips on how consumers can protect themselves
- Monitor your credit reports closely
- Be aware that scammers can use your sensitive information at any time
- Freeze your credit report to halt thieves from opening new credit cards or loans using your name
Equifax Cybersecurity Incident:
“To learn more about the cybersecurity incident, including whether your personal information was potentially impacted, or to sign up for complimentary identity theft protection and credit file monitoring”, please go directly to their site:
https://www.equifax.com/personal/




















You must be logged in to post a comment.