According to HealthIT.gov, cybersecurity is a shared responsibility. “Cybersecurity refers to ways to prevent, detect, and respond to attacks or unauthorized access against a computer system and its information.” To address the problem, the Department of Homeland Security (DHS) is collaborating with public and private partners to promote cybersecurity awareness for all internet users. It is amazing when you hear about DHS collaborating with the Secret Service and the Electronic Crimes Task Forces (ECTFs). It seems surreal and more likely to occur in the movies, but it is happening right now to regular people in their daily lives. We as a society are interconnected and willing to take the risks with technology. We enjoy the accessibility of mobile devices, checking emails, texting, sending photographs, and much more. There are many people who believes that he or she are experts in technology or savvy users. They bend the rules, use their own personal device to do work at the airport, coffee shop, and hotels. This type of person is not always concerned with using unsecured WiFi. This same person might even click on links in any email and might provide their username or password without a second thought.
It is very important to be aware and educated and know when it is necessary to use a VPN for a secure remote access to email and file servers. The word encryption always creeps up. So here are some important terminology and videos to increase awareness.
What is Identity Theft?
There are three types:
- Medical Identity Theft
- Tax-Related Identity Theft
- Child Identity Theft
Medical Identity Theft
According to the FTC a criminal may use your name and health insurance policy number or group plan number to gain access to prescription medications and file claims with your insurance provider. In worst case scenario, the thief might even see a physician and receive care under your name. Your own health information will be mixed up with the thief with negative repercussion. You might receive the wrong medication, diagnosis, etc.
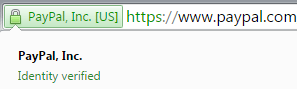
Some other signs might be a bill received for medical services not received, a call from a debt collector on your credit report that you do not recognize, a notice from the health plan stating you reached your benefit limit, a denial of insurance because your medical records show a condition you don’t have. The most important step is to prevent this situation from occurring. Protect your information by not sharing medical or insurance information by phone or email unless you initiated the call and the phone number is known to you. Keep your information in a secured and safe place. If the information is no longer needed, shredding the documents is a must! It is important to read the privacy policy of your physician’s office or their website prior to providing sensitive information online. Ask why the information is needed, how it will be kept safe and will it be shared with others. Always view the URLs prior to trusting the site and make sure they have https where “s” means secure. There are others with extended verification certificates such as PayPal.
There are yellow locks that would show up when the connection is encrypted with modern cryptography but the page includes other resources which are not secure. The information can be viewed by others in transit or can be modified by an attacker to change the look of the page, etc.
Occasionally, I would go to my personal email account and would receive a red https with a red line through it. This typically means there might be something wrong. If this happens, don’t trust the link and close it. Start with a new tab and type the website you want.
But if you already suspect identity theft, then correcting mistakes in your medical record is the first solution. For more information follow this link: http://www.consumer.ftc.gov/articles/0171-medical-identity-theft
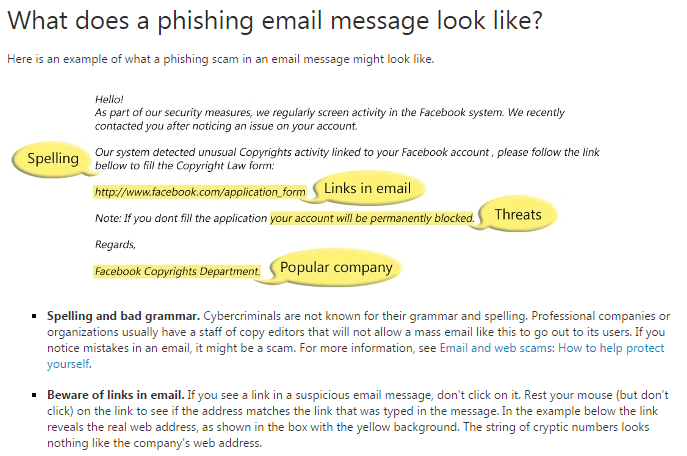
Tax Related Identity Theft
In this scenario, the criminal can use your Social Security Number (SSN) to obtain your tax refund or obtain a job. It is very important to contact the IRS if you received notice that you made money from an employer you don’t know or when you notice that there are more than one tax return filed with your SSN. The first step is to review your tax return. It is important to know that the IRS does not contact taxpayer through email, text or social media message that asks for sensitive information. If you receive this type of email, do not reply or click on any links. The thief is using an activity called phishing by posing as a legitimate company to steal your online account or financial information. The next step to take is to forward the email to phishing@irs.gov.
Here is a good example from Microsoft on online privacy/phishing.
What is cybercrime? Cybercrime is the “illegal activities undertaken by criminals for financial gain” (Detica, 2011, p.1). If you think you have been a victim of cybercrime and your identity is stolen or you have responded to a scam, immediately change the passwords and PINs on all your accounts, and report the incident to your Credit Card Company, bank, or health insurer. You should also report the Identity theft to the U.S. Federal Trade Commission (FTC) at ftc.gov/idtheft. Scams or fraud should be reported to the FTC at ftccomplaintassistant.gov.
View this short video if you think you’ve been a victim of identity theft: http://www.consumer.ftc.gov/media/video-0024-what-if-youre-victim-identity-theft
“One out of every two adults working online has experienced a problem with cybercrime in the last year” according to David Finn (2015), Associate General Counsel & Executive Director, for Microsoft Cybercrime Center.
In the report written by Detica Limited, four areas of focus was mentioned:
- Costs in anticipation of cybercrime and the need for security measures (antivirus solutions, costs of insurance and IT)
- Costs as a consequence from monetary losses, and gaps in business continuity
- Costs in response to cybercrime such as fines and compensation to the identity theft victims
- Indirect costs such as organization’s loss of reputation or loss of revenue from reputational damages
The most important part of the report was the estimated annual cost from cybercrime to be £27bn per annum in the UK or about 43 billion U.S. dollars.
Here’s a short video with many tips on safe practices: https://www.youtube.com/user/MSFTOnlineSafety
Child Identity Theft
Children’s SSN’s can be used by thieves to apply for government benefits, open a bank account, credit card account, apply for a loan, obtain utility service, or rent an apartment. It is very important to ask your child’s school why a sensitive information is required and how is it being stored, used, or thrown out. It is important as parents that you protect your child’s information and decrease the possibility of identity theft.
For more information please view this short video from the FTC: http://www.consumer.ftc.gov/media/video-0060-your-source-truly-free-credit-report-annualcreditreportcom
Come visit with RISC and Virtual Auditor at HIMSS15 in Chicago. Hope to see you there!
References
Detica Limited. (2011). The cost of cybercrime: A Detica Report in partnership with the Office of Cyber Security and Information Assurance in the Cabinet Office. Retrieved from https://www.gov.uk/government/uploads/system/uploads/attachment_data/file/60943/the-cost-of-cyber-crime-full-report.pdf
Finn, D. (2015, January 28). Enterprise Perspectives: Microsoft Cybercrime Center. Retrieved from https://www.youtube.com/watch?v=f28yYIthjoc
Health IT.gov. (2015, January 12). Privacy and security. Retrieved from http://www.healthit.gov/providers-professionals/cybersecurity-shared-responsibility
Homeland Security.(2015, January 7). Cybersecurity. Retrieved from http://www.dhs.gov/topic/cybersecurity
Microsoft. (2014). Safety and Security Center. Retrieved from http://www.microsoft.com/security/online-privacy/phishing-symptoms.aspx






















You must be logged in to post a comment.